| Zero trust security is a modern approach to cyber security that assumes no user, device, or network connection should be trusted by default, regardless of location. Every access request is continuously verified using identity, device health, and context, rather than granted automatically once someone is “inside” the network. |
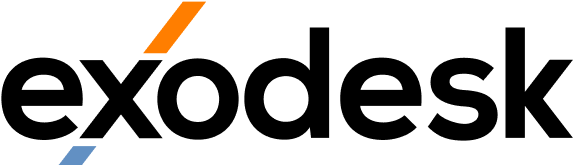
For decades, business cyber security worked like a castle. Build a strong wall (the firewall), check people at the gate, and then trust them once they are inside. That model made sense when staff worked in one office, on company-issued computers, on company-owned networks, accessing company-owned servers. Almost none of those things are true any more.
Staff work from home, from cafes, from clients’ offices, from anywhere with internet. The applications they use live in the cloud rather than in the server cupboard. Customers, contractors, and partners access systems that used to be internal-only. The perimeter has dissolved, but most NZ businesses are still defending it as if it were intact.
Zero trust security is the model that replaces the perimeter. Instead of trusting anything inside a network boundary, it verifies every access request, every time, based on who is asking, what device they are using, and what they are trying to access. This blog covers what zero trust security actually is, why it has become the default for modern cyber security, the core principles, how it works in practice, how to start adopting it, and the misconceptions that trip businesses up. It is written for owners and managers making the strategic call, not for IT teams handling the implementation.
What Is Zero Trust Security?
Zero trust security is a cyber security model built on the principle that no entity should be trusted by default, even if it is inside the corporate network. Every access request is verified explicitly, using multiple signals: who the user is, what device they are on, where they are connecting from, what they are trying to access, and what risk indicators are present at that moment.
The model emerged from a recognition that perimeter-based security keeps failing. Attackers routinely get inside corporate networks (through phishing, supply-chain compromise, or stolen credentials) and then move freely once inside because the network implicitly trusts anything connecting from inside itself. Zero trust security removes that implicit trust entirely.
How is zero trust different from traditional perimeter security?
Traditional perimeter security works on the assumption that the network has a boundary and that everything outside is potentially hostile, everything inside is implicitly trustworthy. Zero trust security works on the opposite assumption: trustworthiness is never implicit, always proven, and always reverified. A user who logged in successfully five minutes ago does not automatically stay trusted; the verification continues throughout the session.
What does “never trust, always verify” mean in practice?
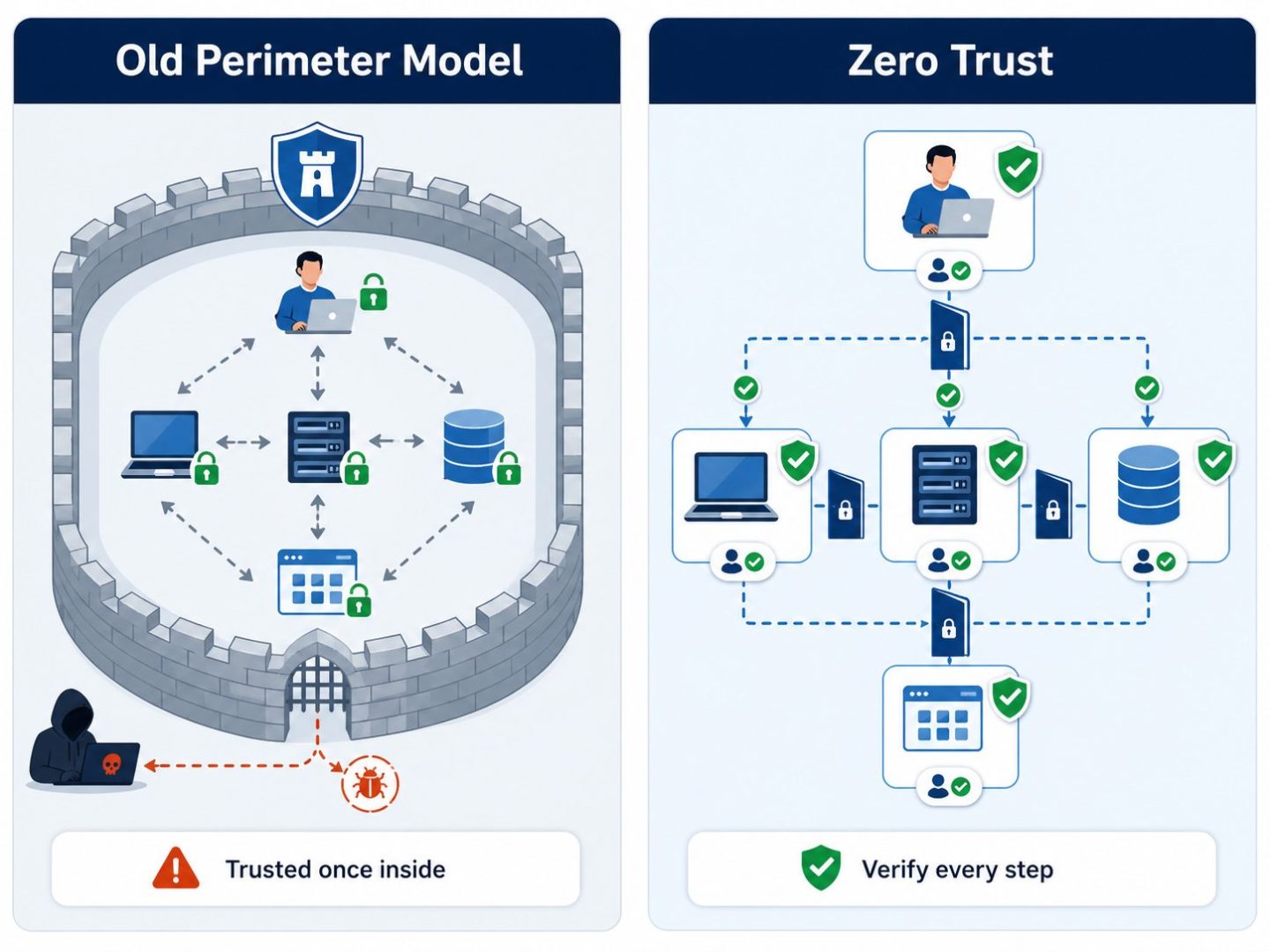
“Never trust, always verify” is the operating principle behind zero trust security. In practical terms, it means every access request is evaluated against current signals: the user’s identity, MFA status, the device’s health (patched, encrypted, managed), the location and time, and the sensitivity of what they are trying to access. Access is granted only when the request meets policy, and policies can require stronger verification for higher-risk requests.
Why Zero Trust Is Now the Default Security Model
Zero trust security has shifted from “advanced practice for large enterprises” to “baseline expectation for any business with cloud services and hybrid working” in the past five years. Three forces have driven the shift: the dissolution of the network perimeter, the recognition that insiders matter as much as outsiders, and the formalisation of zero trust thinking by regulators, insurers, and major vendors.
Cloud and hybrid working broke the old perimeter
When staff work from anywhere and applications live in the cloud, there is no longer a single network boundary to defend. A perimeter security model is defending a wall that no longer surrounds anything meaningful. Zero trust security replaces the wall with a continuous verification model that works equally well regardless of where the user, device, or application happens to be physically located.
Cloud-specific security has its own dynamics. Our blog on Cloud Security covers how zero trust principles apply when workloads sit in Microsoft 365, Azure, or AWS rather than on premises, and why traditional firewall thinking falls short there.
Insider threats are real, even when unintentional
A staff member with a compromised account, or a contractor whose laptop has been infected with malware, becomes an attacker inside the network. Traditional perimeter security has no good answer for this because the threat actor looks like a trusted internal user. Zero trust security limits the damage by verifying every action against policy, rather than assuming an internal user can do anything internal users can do.
Most Insider Threats incidents are not malicious; they are compromised accounts, lost devices, or genuine mistakes. Zero trust security limits the blast radius of all three through least-privilege access and continuous verification.
Compliance, insurance, and customer expectations
Cyber insurers now routinely ask whether the business has adopted zero trust principles before issuing or renewing cover. Regulators increasingly expect zero trust as part of “reasonable” security under privacy legislation. Larger customers ask about it in security questionnaires before signing contracts. The commercial pressure is now significant enough that zero trust security has become a competitive differentiator as much as a defensive one.
The Core Principles of Zero Trust Security
Zero trust security rests on four operating principles, originally formalised by analysts and now embedded in vendor frameworks from Microsoft, Google, and others. Every implementation differs in detail, but the underlying principles stay the same: verify explicitly, use least privilege, assume breach, and monitor continuously.
Verify explicitly
Every access request is authenticated and authorised using all available signals: user identity, device health, location, time, application sensitivity, and behavioural patterns. The verification is explicit rather than implicit. A successful sign-in is not a permanent grant of trust; it is a single decision based on the signals at that moment, and it can be revoked the moment those signals change.
Use least-privilege access
Users and applications get only the access they need for the specific task at hand, nothing more, and only for as long as they need it. This is the operational opposite of the old approach where staff were granted broad access on day one and rarely had it trimmed. Least privilege limits the blast radius of any compromise: an attacker who takes over an account only gets what that account was authorised to do.
Assume breach
Zero trust security designs the environment as though an attacker has already gained some access somewhere. This sounds pessimistic but produces dramatically better outcomes than the alternative. Network segmentation, application-level access controls, monitoring for anomalies, and rapid response capabilities all flow from the assume-breach mindset.
Continuous monitoring and adaptation
Verification is not a one-time event. Zero trust security continuously evaluates whether ongoing access remains appropriate, based on what the user is actually doing, how their device is behaving, and what threat signals the environment is seeing. Access can be tightened, additional verification can be triggered, or sessions can be cut entirely if the signals deteriorate.
How Zero Trust Works in Practice
In practice, zero trust security is delivered through several technology layers working together. The four most important layers for NZ businesses are identity and access management, device health and management, application-level access controls, and network microsegmentation. None of these is exclusive to zero trust, but they have to be configured together with zero trust principles in mind to deliver the security model.
Identity is the new perimeter
In a zero trust model, identity becomes the primary control point. Strong identity providers (Microsoft Entra, Okta, Google) with MFA, conditional access, and continuous risk scoring are the foundation. Without solid identity, the rest of the model does not work. Most NZ businesses already have the building blocks through Microsoft 365 or Google Workspace and simply need to enable and configure them properly.
Device health and management
Access decisions consider device health: is the device managed, encrypted, patched, free of malware? A user trying to access sensitive data from an unmanaged personal device should face different verification than the same user on a corporate laptop with full security controls. Mobile device management and endpoint detection platforms feed this signal into the access policies in real time.
Application-level access
Zero trust security access is granted at the application level rather than network level. Instead of letting a connected user reach any internal system, the user only gets to specific applications they are authorised for, and only through verified, monitored connections. This is a significant shift from traditional VPN models, where a connected user often had broad network reach by default.
Network microsegmentation
Microsegmentation divides the internal network into small zones with explicit policies about what can communicate with what. Even an attacker who lands on one segment cannot move laterally to another without being verified. The technology to do this is now widely available, and combined with the other layers it dramatically limits how far any single compromise can spread.
How to Start Adopting Zero Trust Security
Zero trust security adoption is a journey of several years for most NZ businesses, but the first steps deliver dramatic security improvements in a matter of weeks. The right way to start is not “buy a zero trust product”; it is to take the building blocks the business already has and configure them according to zero trust principles, then build out from there.
Step 1: Map identities and access
Document who has access to what, with what level of privilege, and through which credentials. Most NZ businesses doing this for the first time find significant over-provisioning: users with admin rights they no longer need, service accounts with broad access from years ago, and dormant accounts that should have been disabled. Tidy the inventory first; everything else builds on it.
Step 2: Strengthen identity with MFA and conditional access
Enforce multi-factor authentication on every account, especially admin accounts. Configure conditional access policies so sign-ins from unmanaged devices, unusual locations, or high-risk patterns require additional verification or are blocked entirely. This single phase delivers most of the practical value of zero trust security in the first few weeks of a programme.
Step 3: Verify device health
Deploy mobile device management and endpoint detection across business devices. Configure access policies to check device health (managed, encrypted, patched) before allowing access to sensitive applications. Devices that fail the health check get conditional access or are blocked entirely. This closes one of the largest remaining gaps in most NZ environments.
Step 4: Move from VPN to per-app access
Replace traditional VPN access with application-level access where it makes sense. Tools like Microsoft Entra Application Proxy, Cloudflare Access, or similar zero trust network access products give users direct, verified access to specific applications without giving them broad network reach. This step often takes a couple of quarters to complete, but the security improvement is substantial.
Step 5: Monitor and adapt continuously
Configure the monitoring layer to feed signals back into access decisions: unusual sign-in patterns, anomalous behaviour, malware detections, and data access patterns all become inputs into how the system reacts. The maturity of this loop is what separates a basic zero trust implementation from a strong one, and it builds steadily over time rather than arriving fully formed.
Effective monitoring depends on the people using the system being part of the defence. Employee Security Awareness training matters in a zero trust model because the human response to additional verification prompts is part of how the model holds up against social engineering.
Common Misconceptions and Mistakes About Zero Trust
Zero trust security suffers more than most security models from marketing language and oversimplification. A handful of misconceptions and mistakes recur often enough to be worth addressing directly, because each one quietly undermines an adoption effort.
“Zero trust is a product you buy”
Zero trust is a security model and a set of principles, not a single product. Vendors selling “zero trust solutions” usually offer one important piece of the puzzle (identity, network access, microsegmentation, monitoring) but no single vendor delivers the entire model. Adopting zero trust security means combining several components and operating them with the principles in mind, not buying a box labelled zero trust.
“Zero trust means trusting no one”
The name is misleading. Zero trust security does not mean treating staff as adversaries or making everyone’s daily work harder. It means trust is verified continuously rather than assumed permanently. Done well, the user experience improves: trusted users on healthy devices in familiar locations get smoother access than the old VPN-and-prompt model, with extra verification only triggered when something genuinely looks off.
Trying to do it all at once
Some businesses try to roll out a complete zero trust implementation in a single project. This usually fails because the change is too large to absorb and the layers depend on each other in ways that surprise the team. The successful pattern is incremental: strengthen identity first, then device health, then application access, then network segmentation, then continuous monitoring. Each step is valuable on its own, and earlier steps make later ones easier.
Ignoring the user experience
A zero trust security implementation that prompts users for verification at every turn produces fatigue, workarounds, and eventually staff finding ways around the controls. The right design balances security signals with user experience: high-confidence access (trusted device, normal location, no risk signals) flows smoothly; medium-confidence access asks for one extra factor; low-confidence access asks for more or is blocked outright. The model should reduce friction for legitimate users, not multiply it.
Move Toward Zero Trust Security in Your Business
Zero trust security is the right operating model for any NZ business with cloud applications and hybrid staff, which is now almost every business. The path from current state to a working zero trust environment is a sequence of focused improvements rather than a single project. Exodesk works with businesses across Christchurch, Dunedin, and the South Island to assess current posture against zero trust principles, design the right path forward, and implement it in phases that protect day-to-day operations. Our Cyber Security team brings the strategic, technical, and operational experience needed to make the shift without disruption.
Contact us today to discuss how we can help your business or connect with us on LinkedIn to stay updated with more insights.
Frequently Asked Questions
What is zero trust security in simple terms?
Zero trust security is a cyber security approach that assumes no user, device, or connection should be trusted by default. Every access request is verified explicitly using identity, device health, and context. The principle is “never trust, always verify”, which replaces the old perimeter model where anyone inside the network was implicitly trusted.
How is zero trust different from traditional security?
Traditional security defines a network perimeter and trusts anything inside it. Zero trust security removes that implicit trust and verifies every access request, every time. The shift matters because modern businesses have no real perimeter to defend: staff work from anywhere, applications live in the cloud, and partners connect into internal systems. Zero trust security works in this distributed reality where perimeter thinking fails.
What are the core principles of zero trust?
The four core principles are verify explicitly (every access decision uses multiple current signals), use least-privilege access (users get only what they need, only when they need it), assume breach (design as though an attacker is already inside), and continuously monitor (verification is ongoing rather than one-time). These principles, applied together, define a zero trust security model.
How do you implement zero trust security?
Adoption is incremental rather than a single project. Start with strong identity (MFA, conditional access), then layer in device health verification, then move to application-level access controls, then add network microsegmentation, then build continuous monitoring. Each step delivers real value, and earlier steps make later ones easier. A typical NZ SME journey to a mature zero trust implementation runs across one to three years.
How much does zero trust security cost?
Costs vary widely with current state, business size, and how much of the foundation is already in place. Many NZ businesses on Microsoft 365 already have most of the building blocks (Entra ID, Defender, Intune) and the dominant cost becomes design and configuration rather than new tooling. Specific figures should come from a scoped assessment rather than headline pricing estimates.
Is zero trust security suitable for small businesses?
Yes. Zero trust security is increasingly accessible for NZ SMEs because the building blocks (identity, MFA, device management) are now included in standard business plans of Microsoft 365 and Google Workspace. The implementation is leaner than for large enterprises because the environment is smaller. Small businesses often achieve practical zero trust security faster than large ones, because there is less legacy to unwind.
What tools do you need for zero trust?
The core tooling layers are an identity provider with conditional access (Microsoft Entra ID, Okta, Google), endpoint management and detection (Intune, Defender, similar), application access tooling (Entra Application Proxy, Cloudflare Access, Zscaler), and a monitoring platform that ties the signals together. Most NZ SMEs cover the first three through their existing Microsoft 365 plan and add the others as the programme matures.
Does zero trust replace VPN?
In most cases yes, eventually. Traditional VPNs grant broad network access once a user connects, which is the opposite of zero trust thinking. Zero trust network access (ZTNA) tools replace VPNs with per-application access that is continuously verified. Many businesses run both during the transition, but the long-term direction is clearly away from VPN and toward zero trust security access.
How long does it take to adopt zero trust?
A useful baseline (strong identity, MFA, conditional access, device health checks) can be in place within a few months. A mature zero trust security implementation covering identity, devices, applications, microsegmentation, and continuous monitoring typically takes one to three years to build out. The pace is set by business priorities and existing maturity rather than by the technology itself.
What are common mistakes when adopting zero trust?
The most common mistakes are treating zero trust as a single product purchase, trying to roll out the full model in one project, ignoring user experience and producing fatigue, and skipping the identity foundation in favour of more visible network controls. Avoiding these four covers most of the practical problems NZ businesses run into. An incremental, identity-first approach with attention to user experience produces the best outcomes.