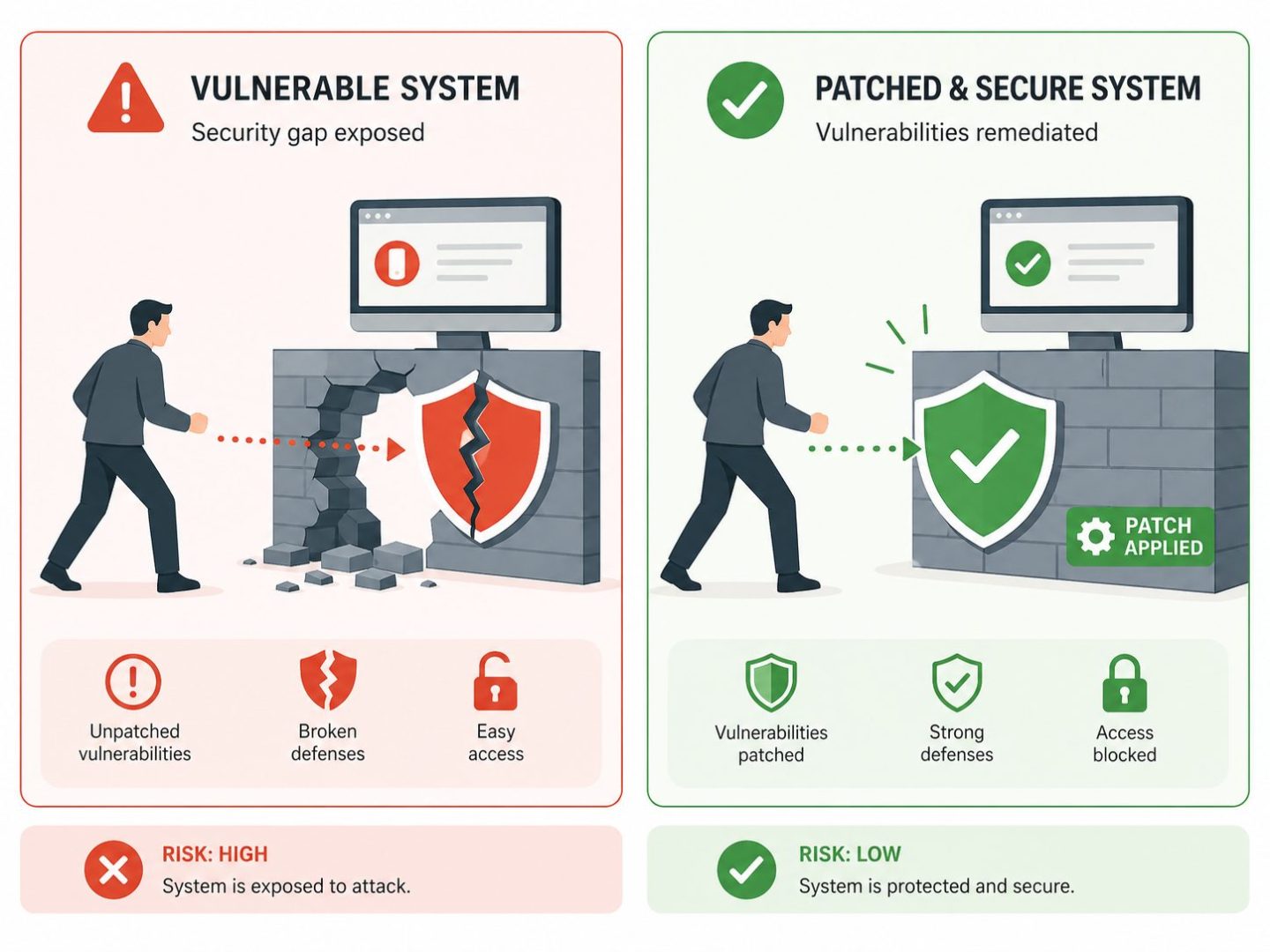
| Vulnerability management is the continuous process of finding, assessing, prioritising, fixing, and verifying security weaknesses across a business technology environment. It is one of the most-skipped cyber security disciplines in NZ SMEs, and one of the most effective at preventing breaches because most attacks exploit weaknesses that were known and fixable. |
The uncomfortable truth about cyber security is that most successful attacks against NZ businesses do not use new, exotic techniques. They use known vulnerabilities in commonly used software, where a patch has existed for weeks, months, or sometimes years. The vulnerability sat in the environment because no one was systematically looking for it.
A disciplined approach is what closes this gap. It is the structured process of finding every weakness before an attacker does, deciding which ones matter, fixing or mitigating them, and verifying that the fix actually worked. Done well, it dramatically reduces the surface that attackers can exploit. Done badly or not at all, it leaves the door propped open while everyone else focuses on more visible security work.
This blog covers what vulnerability management actually is, why it matters for NZ businesses, the lifecycle that turns scanning into real risk reduction, how to prioritise fixes effectively, the tools involved, and the common mistakes that turn the programme into spreadsheets nobody reads. It is written for owners and managers making the investment decision, not for IT teams handling the implementation.
What Is Vulnerability Management?
Vulnerability management is the continuous, structured process of identifying security weaknesses in a business technology environment, assessing how serious each one is, fixing or mitigating them, and verifying that the fix worked. It runs across servers, end-user devices, network equipment, applications, cloud services, and increasingly the third-party software components that those systems depend on.
The key word is “continuous”. New vulnerabilities are disclosed every day, new software is deployed constantly, and configurations drift over time. A one-off security audit gives a snapshot of one moment in time and becomes outdated almost immediately. The discipline is ongoing operational work, not a project.
How does vulnerability management differ from patch management?
Patch management is the narrower discipline of applying software updates to fix known issues. Vulnerability management is broader and includes finding weaknesses that patching alone cannot fix: misconfigurations, weak credentials, exposed services, insecure code in custom applications, and third-party components inside the software you use. Patching is part of the picture, but not all of it. Many of the most damaging breaches in recent years exploited weaknesses that no patch could have prevented.
What counts as a vulnerability?
A vulnerability is any weakness in a system that an attacker can exploit to gain unauthorised access, escalate privileges, steal data, or disrupt operations. Common examples include unpatched software, default or weak passwords, misconfigured firewalls, exposed admin interfaces, insecure file permissions, and outdated cryptographic protocols. The full list is wide and grows constantly as researchers and attackers find new patterns.
Why Vulnerability Management Matters for NZ Businesses
Vulnerability management matters because the vast majority of successful cyber attacks exploit weaknesses that were known and could have been fixed before the attack happened. A disciplined programme closes that gap, and the cost of doing so is dramatically lower than the cost of being breached.
Most breaches exploit known, fixable weaknesses
Year after year, breach reports from major NZ and international sources show the same pattern: most successful attacks use vulnerabilities that had patches or mitigations available, often for months before the breach. The attacker did not have to be clever; they just had to find a business that had not done its vulnerability management work. A disciplined programme removes the easiest targets first, which is also the targets that attackers preferentially go after.
This is why a regular Cybersecurity Risk Assessment that includes vulnerability scanning across the environment is now considered baseline practice rather than an enhanced service.
The cost asymmetry
A managed vulnerability programme costs a fraction of what a single significant breach costs in incident response, downtime, customer communication, regulator engagement, and reputational damage. The disparity is dramatic. For NZ SMEs in particular, where a serious cyber incident can be existential, the cost calculation is unusually one-sided in favour of investing upfront.
Most ransomware incidents begin with the exploit of an unpatched vulnerability. The lurid stories that circulate are useful but our Ransomware Myths blog clears up the common misconceptions and shows how disciplined remediation work changes the probability calculus more than almost any other single control.
Insurance, compliance, and customer expectations
Cyber insurers now ask explicit questions about vulnerability management practices before issuing or renewing cover. Regulators expect it for systems handling personal data under the NZ Privacy Act. Larger customers increasingly ask about it in security questionnaires before signing contracts. The cost of not having a vulnerability management programme has shifted from “potential risk” to “concrete commercial obstacle”.
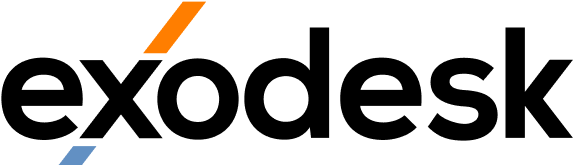
The Vulnerability Management Lifecycle
A working vulnerability programme follows a five-step lifecycle: discover, assess, remediate, verify, and continuously improve. Each step has to work for the next to be meaningful, and skipping any step turns the whole programme into a scanning report nobody acts on.
Step 1: Discover and inventory
You cannot protect what you do not know about. The first step is a complete inventory of every device, system, application, and cloud service in the business technology environment. Most NZ businesses doing this honestly for the first time find systems they had forgotten about, often the ones running on the oldest, most vulnerable software. Discovery should run continuously rather than once, because the environment changes constantly.
Step 2: Assess and prioritise
Scan every asset for known vulnerabilities and misconfigurations. Modern vulnerability scanners maintain databases of hundreds of thousands of known issues and check each system against them. The output is a list, often a long one. The work then becomes prioritisation: not every vulnerability needs to be fixed in the next 24 hours, and trying to fix everything at once means nothing gets fixed properly.
Step 3: Remediate or mitigate
For each prioritised vulnerability, choose whether to fix it (apply a patch or change a configuration), mitigate it (add compensating controls that reduce the risk without removing the underlying weakness), or accept it (document the risk and move on, usually only valid for low-impact issues). Most issues get fixed; some get mitigated; very few should ever be accepted without a clear, documented reason.
Step 4: Verify the fix
A fix that was not verified is a fix that might not have worked. After remediation, re-scan to confirm the vulnerability is genuinely closed. This step is the one most often skipped, and the one where the most damage happens when something goes wrong. Patches occasionally fail, configurations occasionally revert, and the only way to know is to look again.
Step 5: Report and continuously improve
Track metrics over time: how many vulnerabilities exist, how quickly they are fixed by severity, which systems carry the most risk, and how the trend looks month to month. The reporting is what turns the programme from a series of scans into an operational discipline that improves year on year. Without it, vulnerability management drifts back into reactive mode and loses most of its value.
How to Prioritise Vulnerabilities Effectively
The hardest part of any such programme is prioritisation. A medium-sized NZ business will typically have thousands of open vulnerabilities at any moment, far more than can be fixed immediately. Effective prioritisation combines technical severity scores with exploitability, asset criticality, and business context to focus effort where it actually reduces risk.
CVSS scores and what they tell you
The Common Vulnerability Scoring System (CVSS) assigns each known vulnerability a severity score from 0 to 10, broken into Critical, High, Medium, and Low. CVSS is useful as a starting point but is not the full answer. It does not know which systems matter most to your business, whether the vulnerability is being actively exploited in the wild, or whether other controls in the environment make exploitation harder.
Exploitability matters as much as severity
A High-severity vulnerability that requires local access and specific user actions is meaningfully less urgent than a Medium-severity one that can be exploited remotely with no authentication and is being weaponised right now. Resources like CISA’s Known Exploited Vulnerabilities catalogue surface which issues are being actively used by attackers. Anything on that list should be fixed urgently, regardless of CVSS score.
Asset criticality and business context
A Critical-severity vulnerability on a test server with no production data is less urgent than a Medium-severity vulnerability on the system that handles customer payments. Effective prioritisation has to layer business context on top of technical severity. A simple way to do this is to tag every asset by criticality (low / medium / high / crown jewel) and score the combined risk per vulnerability accordingly.
When to fix, when to mitigate, when to accept
Fix is the default. Mitigate when fixing is genuinely impossible (legacy system, vendor dependency) or when the fix carries unacceptable operational risk. Accept only when both fixing and mitigating are not viable and the residual risk is genuinely low, with explicit documentation of why. The pattern that produces incidents is treating acceptance as the default for difficult vulnerabilities and never returning to them.
Tools and Approaches for Vulnerability Management
Effective scanning and remediation uses several complementary approaches, not just one tool. The main components are authenticated and unauthenticated scanning, external attack surface management, cloud-native scanning, and penetration testing. Each covers a different angle, and a complete programme uses several together.
Authenticated vs unauthenticated scans
Unauthenticated scans probe systems from the outside without logging in, which approximates what an external attacker would see. Authenticated scans log into each system and can see installed software, configurations, and patches that are invisible from outside. Authenticated scans find dramatically more issues, but require credentials and careful change control. Most mature programmes use both: authenticated for depth, unauthenticated for the outside view.
External attack surface management
External attack surface management (EASM) continuously monitors what the internet sees of your business: domains, public IPs, exposed services, forgotten subdomains, cloud assets that were spun up and forgotten. NZ businesses repeatedly find assets in their external surface they had no idea existed, often dating back years. EASM keeps the outside view continuously fresh rather than relying on point-in-time scans.
Cloud-native vulnerability management
Modern cloud environments need vulnerability management built specifically for the way they work. Cloud configurations, container images, serverless functions, and identity permissions all create vulnerabilities that traditional scanners miss. Cloud-native tools integrate directly with Azure, AWS, and Google Cloud APIs to see what is actually deployed and how it is configured.
Penetration testing as a complement
Vulnerability scanning identifies known issues at scale. Penetration testing applies human creativity to chain vulnerabilities together, find logic flaws no scanner can detect, and validate that the fixes actually work in practice. The two are complementary: scanning at the breadth, pen testing at the depth. An annual penetration test on top of monthly scanning is the standard rhythm for most NZ SMEs taking security seriously.
Common Vulnerability Management Mistakes
A handful of mistakes recur in these programmes across NZ businesses, and each one quietly undermines the effort. Recognising them early prevents the slow drift from disciplined programme back into reactive break-fix work.
Scanning without acting
The most common failure pattern is buying a scanner, generating reports, and never closing the loop on remediation. The scans produce data; nobody owns the work of acting on it. The fix is to assign clear ownership for remediation at the start, with target timelines by severity, and to track those timelines as a programme metric rather than treating reports as the deliverable.
This is exactly the kind of discipline a Proactive IT approach delivers consistently, where scanning, prioritisation, remediation, and verification happen as part of normal monthly operations rather than as a series of disconnected projects.
Treating high-CVSS as the only priority
Focusing on Critical and High CVSS scores misses two important things: Medium-severity vulnerabilities that are actively being exploited in the wild, and combinations of lower-severity issues that chain together into a serious attack. Real prioritisation combines technical severity with exploitability and business context, not just the headline score.
Ignoring third-party libraries and SaaS
Most modern applications include dozens or hundreds of third-party libraries, each of which can contain vulnerabilities. A scan of your own code that ignores these components misses a substantial portion of the actual risk. SaaS platforms have their own vulnerability management responsibilities, but customers also need to track the assets, integrations, and configurations they own in those platforms.
Not verifying remediation
Closing a vulnerability without re-scanning is a leap of faith. Patches occasionally fail to apply, configuration changes occasionally revert, and the supposed fix occasionally introduces new issues. The verification step closes the loop and catches these gaps before an attacker does. Skipping it is one of the most common reasons “patched” environments still get breached.
Build Vulnerability Management Into Your Operations
Vulnerability management is one of the highest-leverage cyber security investments any NZ business can make, but only when it is treated as an ongoing operational discipline rather than a one-off project. Exodesk works with businesses across Christchurch, Dunedin, and the South Island to build vulnerability management programmes that scale with the business, prioritise effectively, and turn scanning data into real risk reduction. Our Managed IT Services include continuous vulnerability scanning, prioritised remediation, and the reporting cadence that keeps the programme producing value year on year.
Contact us today to discuss how we can help your business or connect with us on LinkedIn to stay updated with more insights.
Frequently Asked Questions
What is vulnerability management in simple terms?
Vulnerability management is the continuous process of finding security weaknesses in your business technology, deciding how serious each one is, fixing or mitigating them, and verifying that the fix worked. It runs across servers, devices, applications, and cloud services. Done well, it dramatically reduces the surface that attackers can use to breach the business.
What is the difference between vulnerability management and patch management?
Patch management is the narrower discipline of applying software updates. Vulnerability management is broader and includes finding misconfigurations, weak credentials, exposed services, insecure third-party components, and code issues that no patch can fix. Patching is one part of vulnerability management, but a vulnerability management programme covers everything that patching alone misses.
What is a vulnerability scanner?
A vulnerability scanner is a tool that automatically checks systems against databases of known security weaknesses and misconfigurations. Common business-grade options include Tenable Nessus, Qualys, Rapid7 InsightVM, and Microsoft Defender Vulnerability Management. The scanner produces a report of issues found, which is the starting point for the rest of the vulnerability management process.
How often should I scan for vulnerabilities?
Best practice is continuous or at minimum monthly scanning of every asset in the environment. Critical systems benefit from daily or weekly scans, and new systems should be scanned before going into production. Annual scans are not enough because new vulnerabilities are disclosed every day. The right cadence depends on the size and criticality of the environment, but more frequent is almost always better than less frequent.
How much does vulnerability management cost?
Costs vary significantly with the number of assets, the tooling chosen, and whether the work is run internally or through a managed service. Vulnerability scanner pricing is set by the vendors and changes periodically, so meaningful current figures come from a scoped assessment rather than older sources. The dominant cost is usually the staff time to triage and remediate findings, not the tool itself.
Is vulnerability management the same as penetration testing?
No. Vulnerability management is the ongoing programme of scanning and fixing known weaknesses across the environment. Penetration testing is a point-in-time exercise where ethical hackers actively try to break in, often chaining lower-severity issues together into a serious attack. The two are complementary: vulnerability management for breadth and continuity, penetration testing for depth and validation.
Which vulnerabilities should I fix first?
Fix highest-priority vulnerabilities first, which means combining technical severity with exploitability and business context. A Medium-severity vulnerability being actively exploited in the wild on a critical business system is more urgent than a Critical-severity issue on an isolated test environment. The CISA Known Exploited Vulnerabilities catalogue is a useful real-time signal of what attackers are using right now.
What tools do I need for vulnerability management?
At minimum you need a vulnerability scanner that covers your environment, an asset inventory, and a way to track remediation work. Mature programmes add external attack surface management, cloud-native scanning, and periodic penetration testing. Many NZ SMEs achieve the right balance through a managed service rather than building the internal capability from scratch, which is usually faster and cheaper to get right.
Does the NZ Privacy Act require vulnerability management?
The Privacy Act 2020 requires reasonable security safeguards for personal information, and vulnerability management is now widely considered part of “reasonable” practice. There is no specific clause that names vulnerability management directly, but a serious privacy breach caused by a known, unpatched vulnerability would be hard to defend as having taken reasonable precautions. Effectively, the discipline has crossed into baseline expectation territory.
How do we start with vulnerability management?
Start with an asset inventory of every device, system, application, and cloud service the business uses. Run an initial vulnerability scan to establish a baseline, then prioritise the top findings and assign clear remediation ownership. Build the lifecycle into a monthly operational rhythm rather than treating it as a one-off project. An experienced IT partner can typically have a useful programme running within a few weeks rather than months.