| Multi factor authentication (MFA) is a security control that requires users to prove their identity with more than one factor before being granted access to a system. It blocks the vast majority of credential-based attacks at almost no operational cost, which is why it has become the single highest-value security control most NZ businesses can deploy. |
If you were going to do one thing this quarter to materially reduce cyber risk in your business, multi factor authentication would be it. Not the latest security platform, not a new firewall, not an awareness campaign. Just MFA, enforced everywhere, on every account that matters.
Microsoft research has consistently shown that enabling MFA blocks more than 99 percent of automated account-takeover attempts. That is not a marketing figure from a vendor; it is years of data from one of the largest identity providers in the world. Few security controls in any other area of business come anywhere near that effectiveness for the effort involved.
This blog covers what multi factor authentication actually is, why it has become non-negotiable, the different types you can use, the common implementation mistakes, how to roll it out across a business, and the newer phishing-resistant methods that improve on traditional MFA. It is written for owners and managers making the decision, not for IT teams handling the configuration.
What Is Multi Factor Authentication?
Multi factor authentication is a sign-in process that requires users to present at least two pieces of evidence (factors) to verify their identity. A password alone is one factor; adding a code from a phone app or a tap on a hardware key creates a second factor. The presence of two independent factors stops an attacker who only has one of them, even if that one is the password.
The strength of MFA comes from its asymmetry. Defending an account with MFA is straightforward and adds seconds to the sign-in process. Attacking an MFA-protected account is dramatically harder than attacking a password-only account because the attacker has to compromise something physical or in real time, not just guess or buy a leaked password from a forum.
How does multi factor authentication work in practice?
At sign-in, the user enters their username and password as the first factor. The system then prompts for the second factor: a code from an authenticator app, a tap on a push notification, a biometric like a fingerprint, or a touch on a hardware security key. Only when both factors verify successfully does the system grant access. The whole experience adds a few seconds for the user and dramatically more work for an attacker.
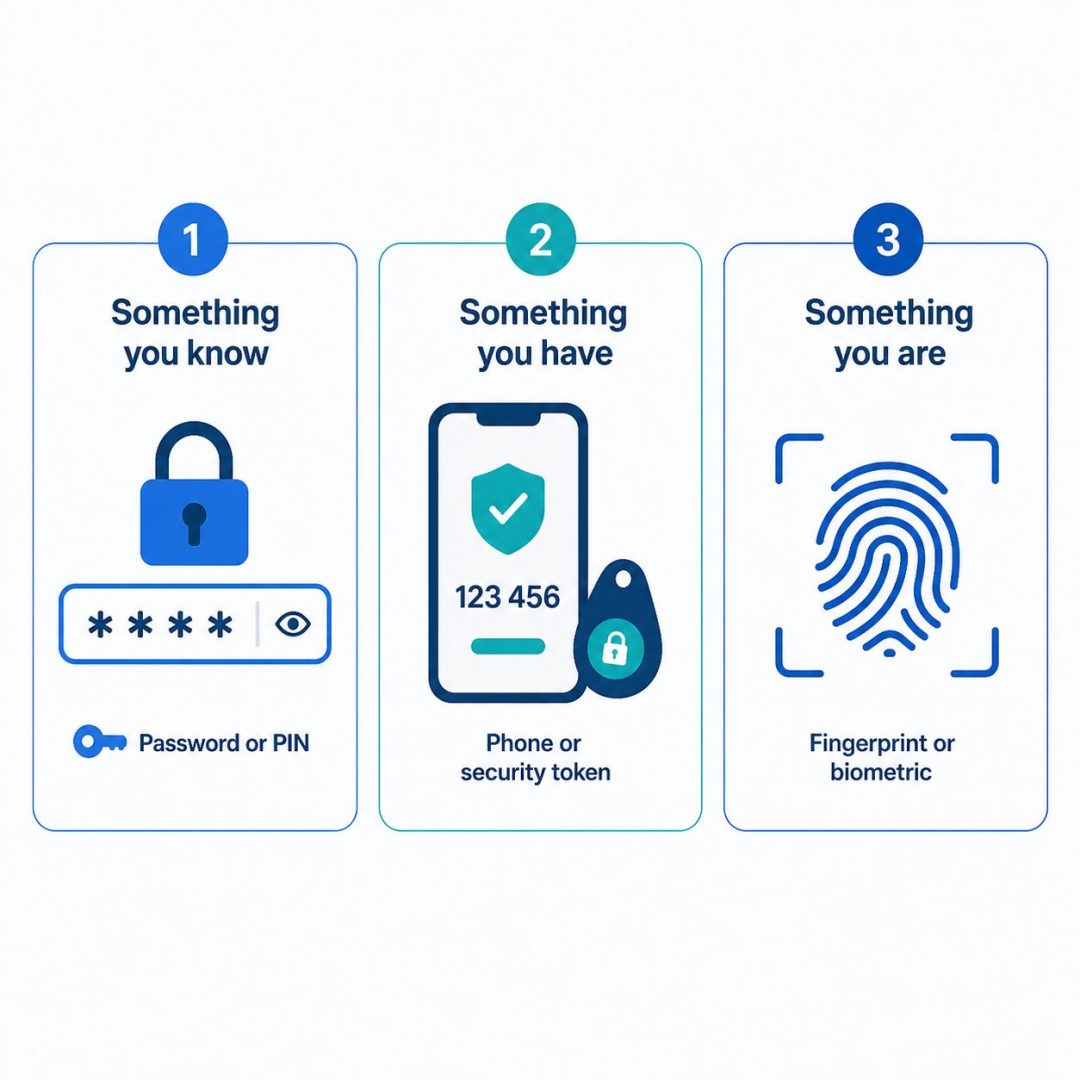
What are the three authentication factors?
The three categories are something you know (a password or PIN), something you have (a phone, security key, or smart card), and something you are (a fingerprint, face, or other biometric). Multi factor authentication requires factors from at least two of these categories. Using two passwords does not count as MFA because both factors come from the same category and share the same weaknesses.
Why Multi Factor Authentication Is Non-Negotiable Today
Multi factor authentication has shifted from a recommended best practice to a baseline expectation in cyber security. Three forces have driven the change: the collapse of password security, the scale of credential-based attacks against NZ businesses, and the expectations of insurers, regulators, and increasingly customers.
Passwords alone are no longer enough
Passwords leak. They are reused across sites, written down, phished, stolen through malware, and traded in bulk on the dark web. The honest assumption every business should make today is that the passwords used by your staff are already, or will be, known to attackers somewhere. That is not pessimism; it is the operating reality of the modern internet. MFA is the layer that makes the leaked password ineffective on its own.
The scale of credential leakage is constant. Dark Web Monitoring services regularly find business email addresses paired with passwords in dumps from breaches the affected companies never had any direct connection to. Multi factor authentication is what makes those leaked passwords useless to the people who bought them.
The numbers behind credential-based attacks
Credential-based attacks (where the attacker uses a working username and password rather than exploiting a software vulnerability) are now the most common way NZ businesses are breached. Phishing for credentials, password spraying, and brute-force guessing against exposed services all bypass everything else in your security stack if they succeed. Multi factor authentication is the single control that breaks the entire attack class.
Compliance, insurance, and customer expectations
Cyber insurers now routinely require MFA on email, remote access, and admin accounts before issuing or renewing cover. Regulators expect it on systems handling sensitive data. Customers increasingly ask about it in security questionnaires before signing contracts. Multi factor authentication has crossed the threshold from “we should probably do this” to “the cost of not doing this is now higher than the cost of doing it”.
The Different Types of MFA and Which Are Strongest
Not all MFA is equal. The methods range from weak (SMS codes) to strong (hardware keys and passkeys), with several options in between. Choosing the right method per risk level matters more than turning on any kind of MFA and considering the job done.
SMS-based codes (weakest)
A code is sent by SMS to the user’s phone. It is widely supported and easy for users, which is why many businesses started here. The problem is SIM-swap attacks, where an attacker takes control of the target’s phone number through social engineering of the mobile carrier, and intercepts the codes. SMS MFA is meaningfully better than no MFA at all but should not be the only method on accounts that matter.
Authenticator apps (good baseline)
Apps like Microsoft Authenticator, Google Authenticator, or Authy generate time-based codes on the user’s phone. The code is generated locally on the device rather than sent over the air, which removes the SMS interception risk entirely. Authenticator apps are free, work offline, and are the right baseline for almost every NZ business.
Push notifications with number matching
A push notification arrives on the user’s phone asking them to approve or deny a sign-in attempt, often with a number they have to match from the sign-in screen. The number-matching step is important: it prevents users from absent-mindedly approving prompts from attackers, which is a real attack pattern known as MFA fatigue. Push with number matching is one of the strongest broadly-deployable methods available today.
Hardware security keys (strongest broadly available)
Physical keys like YubiKey or Google Titan plug into a USB port or tap against a phone to complete sign-in. They are phishing-resistant by design because the cryptographic exchange is bound to the actual website the user is signing in to, not to whatever the user might have been tricked into clicking. Hardware keys are the right choice for admin accounts, executive accounts, and any role that handles particularly sensitive information.
Passkeys and the future of authentication
Passkeys are a newer technology that combines the security of hardware keys with the convenience of biometrics, stored across the user’s devices. They are gradually being adopted by major platforms (Microsoft, Google, Apple, Microsoft 365). Passkeys are likely to replace passwords entirely over the next several years, with multi factor authentication folded into the underlying design rather than added on as a separate step.
Common Multi Factor Authentication Implementation Mistakes
Most MFA-related breaches in NZ businesses happen not because MFA failed, but because it was implemented incompletely or incorrectly. Four mistakes recur often enough to be worth calling out specifically.
Leaving admin accounts without enforced MFA
Admin accounts are the highest-value target in any environment, yet they are often the accounts where multi factor authentication is treated as optional because the admin “trusts themselves”. This is precisely the wrong instinct. Admin accounts must be the first accounts protected with the strongest available MFA method, ideally hardware keys. Compromise of an admin account is materially worse than compromise of any user account.
Allowing SMS as the primary method on critical accounts
SMS MFA on customer-facing accounts handling personal data, or on admin accounts, leaves a clear vulnerability open. The fix is straightforward: enable authenticator apps or push notifications as the default, and reserve SMS as a fallback only for accounts where stronger options genuinely are not available. Most modern business platforms support stronger methods.
Not enforcing MFA across every app
Many businesses turn MFA on for email and consider the job done. Attackers love this. Single sign-on solutions, accounting platforms, CRM systems, and any business application with internet-facing access need MFA too. An attacker who finds a single app without MFA can use it as a foothold into the wider environment.
This is exactly where Defence in Depth thinking matters. MFA on one app is helpful; MFA across every important app is what closes the gaps attackers actively look for.
Not protecting against MFA fatigue attacks
MFA fatigue is an attack where the attacker, who already has the password, repeatedly triggers push notifications until the user approves one out of frustration or distraction. Number matching, conditional access policies that block sign-ins from suspicious locations, and user training are the right defences. Without them, push-based MFA can be defeated by patience.
This is fundamentally a Social Engineering problem rather than a technical one, which makes user training as important as the technical controls themselves.
How to Roll Out Multi Factor Authentication Across the Business
A successful MFA rollout takes two to six weeks for an NZ SME, depending on the number of systems and users involved. The work breaks into five phases: audit current authentication, choose methods per risk level, phase the rollout with training, configure conditional access policies, and plan for recovery and exceptions.
Step 1: Audit current authentication
Document every system the business uses that has its own login, who has access, and what MFA (if any) is currently enforced. Most NZ businesses doing this audit for the first time find several systems without MFA that nobody had thought about, and several accounts (former staff, contractors) that should have been disabled. Address both before moving on.
Step 2: Choose methods per risk level
Match the MFA method to the value of what it protects. Standard staff accounts get authenticator apps or push with number matching. Admin and executive accounts get hardware security keys. Customer-facing accounts handling personal data get strong MFA matched to the sensitivity of the data. Designing for risk level rather than applying one method everywhere produces a stronger, more usable system.
Step 3: Phase the rollout with training
Roll out in waves rather than overnight. Start with IT and senior leadership, then expand to one or two pilot teams, then go business-wide. Each wave gives the rollout team a chance to refine the user communications, fix any platform-specific issues, and build a small group of internal champions who can help colleagues with the change.
Step 4: Configure conditional access policies
Conditional access takes multi factor authentication further by varying the requirement based on context. Sign-ins from trusted devices in trusted locations might require less; sign-ins from a new country or unmanaged device might require a stronger MFA method or be blocked entirely. The right policies make MFA both stronger and less intrusive for staff in their normal patterns.
Step 5: Plan for account recovery and exceptions
Users will lose phones, replace devices, and occasionally lock themselves out. A clear, secure account recovery process avoids the temptation to disable MFA for a quick fix. Document who is authorised to reset MFA, how identity is verified before a reset, and how the process is logged. Without this, the help desk becomes the easiest social engineering target in the business.
Multi Factor Authentication and Phishing-Resistant Methods
Traditional multi factor authentication blocks the vast majority of credential-based attacks but is not entirely phishing-proof. Sophisticated phishing kits can now intercept MFA codes and push approvals in real time. Understanding what phishing-resistant MFA looks like, and when to invest in it, is the next frontier for businesses that have already deployed baseline protection.
Why traditional MFA can still be phished
Adversary-in-the-middle phishing kits create a fake login page that proxies in real time to the legitimate service. The user enters their password and MFA code on the fake site, the kit relays both to the real service, and the attacker captures the resulting session token. Traditional MFA codes (SMS, TOTP from an authenticator app) all work this way: they verify the user, but not the website.
What phishing-resistant MFA looks like
Phishing-resistant MFA cryptographically binds the authentication to the actual website domain. Hardware security keys using FIDO2/WebAuthn, and passkeys, are both phishing-resistant by design. A YubiKey will simply refuse to authenticate against a fake site because the cryptographic exchange does not match the expected domain. This breaks the entire adversary-in-the-middle attack pattern.
When to invest in phishing-resistant MFA
Start with the accounts that would do the most damage if compromised: domain admins, finance approvers, executive accounts, and any account with broad access to customer data. Equip these with hardware keys or passkeys. Standard staff accounts can stay on app-based MFA with number matching for now, with a path to passkey adoption as platforms mature. The cost of hardware keys for high-value accounts is small relative to the risk they cover.
Make Multi Factor Authentication a Standard, Not a Project
Multi factor authentication is one of the rare cyber security controls where the cost is low, the implementation is fast, and the impact is dramatic. The businesses that resist it eventually pay for that resistance, usually in an incident report. Exodesk works with businesses across Christchurch, Dunedin, and the South Island to design MFA strategies that fit the business, roll them out cleanly, and embed them as part of normal operations. Our Cyber Security team covers everything from initial assessment through to ongoing monitoring and support.
Contact us today to discuss how we can help your business or connect with us on LinkedIn to stay updated with more insights.
Frequently Asked Questions
What is multi factor authentication in simple terms?
Multi factor authentication (MFA) is a sign-in process that requires users to present at least two pieces of evidence before being granted access to a system. The factors are something you know (a password), something you have (a phone or hardware key), and something you are (a fingerprint or face). Requiring two of these makes a stolen password useless on its own.
What is the difference between MFA and 2FA?
Two-factor authentication (2FA) requires exactly two factors. Multi factor authentication is the broader term that covers two or more factors. In everyday business use the terms are often used interchangeably, but technically 2FA is a specific subset of MFA. The security principle and the typical user experience are the same in both cases.
How does multi factor authentication actually work?
At sign-in, the user enters their username and password as the first factor. The system then prompts for a second factor: a code from an authenticator app, a push notification approval, a biometric, or a tap on a hardware key. Only when both factors verify successfully is access granted. The user experience adds a few seconds; the attacker experience becomes dramatically harder.
Which type of MFA is the strongest?
Hardware security keys and passkeys are the strongest forms of multi factor authentication because they are phishing-resistant by design. They cryptographically bind authentication to the actual website domain, so they refuse to authenticate against fake sites. For high-value accounts (admins, executives, finance approvers) these are now considered the appropriate standard.
Is SMS-based MFA safe to use?
SMS-based MFA is meaningfully better than no MFA but is the weakest of the common methods. SIM-swap attacks, where an attacker takes control of a target’s phone number through social engineering of the mobile carrier, can intercept SMS codes. SMS is acceptable for low-risk accounts but should be replaced with an authenticator app or push notifications on anything that matters.
Can multi factor authentication be bypassed?
Traditional MFA can be bypassed by sophisticated attacks like adversary-in-the-middle phishing kits, MFA fatigue spam, and SIM-swap attacks against SMS codes. Phishing-resistant methods (hardware keys, passkeys) defeat all of these because they bind authentication to the legitimate website domain. Even with traditional MFA, attackers find it dramatically harder than attacking password-only accounts.
What apps should I use for MFA?
Microsoft Authenticator, Google Authenticator, and Authy are the most common business-friendly options, and all three are free. Microsoft Authenticator integrates particularly well with Microsoft 365 environments, which is the dominant platform for NZ SMEs. Pick one and standardise on it across the business rather than letting staff choose differently.
How much does multi factor authentication cost?
Software-based MFA (authenticator apps, push notifications) is typically included at no extra cost in Microsoft 365, Google Workspace, and most modern business platforms. Hardware security keys cost a small amount per key. The dominant cost is staff time for rollout and training rather than the technology itself. Pricing changes over time so current figures should come from the vendor.
How long does it take to set up MFA for a business?
A typical NZ SME can deploy multi factor authentication across email and core systems in two to six weeks. The timeline is set by how many systems need MFA enabled, how training is staged, and how account recovery processes are designed. The technical work itself is usually faster than the change management around it.
Is multi factor authentication required by law in NZ?
There is no single NZ law that specifically requires multi factor authentication, but the Privacy Act 2020 requires reasonable security safeguards for personal information, and MFA is now widely considered part of “reasonable” practice. Specific sectors (financial services, healthcare) have stronger expectations, and cyber insurers usually require MFA before issuing or renewing cover. In practical terms, MFA has become a baseline expectation rather than an option.