| Network security is the discipline of protecting the connections, traffic, and devices that make up a business network from unauthorised access, attack, and misuse. It includes firewalls, intrusion prevention, segmentation, secure remote access, and the monitoring that ties them together. The goal is to stop threats at the edge before they reach business systems. |
The network is the highway that carries every piece of business data, every staff login, every customer transaction, and every email. It is also the highway that carries every attempted attack, every malicious payload, and every attempt at credential theft. Defending the highway matters as much as defending the destinations.
Some commentators argued in the late 2010s that the rise of cloud computing would make traditional network defences obsolete. The reality has been the opposite: as businesses spread across cloud services, home offices, and partner connections, the network has become more important, not less. The perimeter has shifted shape, but the discipline of controlling traffic, verifying connections, and watching for trouble remains foundational.
This blog covers what network security actually means today, why it still matters in a cloud-first world, the layers that make up a modern programme, how those layers work in practice, how to build a programme without ripping everything out, and the common mistakes that turn a network defence into a quiet liability. It is written for owners and managers making the strategic call, not for IT teams handling the configuration.
What Is Network Security?
Network security is the discipline of protecting the connections and traffic that flow through a business technology environment. It combines preventive controls (firewalls, secure web gateways, intrusion prevention systems), structural controls (segmentation, access policies), and monitoring controls (traffic inspection, anomaly detection, incident response). Together these stop threats from reaching critical systems, contain damage when something does get through, and provide visibility into what is happening across the environment.
The discipline has evolved significantly over the past decade. Old-style firewalls that allowed or blocked traffic based on port numbers are no longer enough. Modern controls inspect what is actually happening inside each connection, identify malicious patterns regardless of the protocol, and integrate with threat intelligence to spot newly emerging risks in near real time.
What does it protect against?
The list is long and growing. External attackers attempting to break in, malware trying to communicate with command and control servers, ransomware spreading laterally once inside, data being exfiltrated to suspicious destinations, denial-of-service traffic overwhelming a service, compromised insider devices reaching where they should not, and the steady background hum of automated probes scanning every public service on the internet. A working set of controls addresses all of these at different points in the traffic flow.
How is network security different from endpoint security?
Endpoint security protects individual devices: laptops, phones, servers. Network security protects the connections between those devices and the systems they reach. The two are complementary rather than overlapping: an attacker who bypasses endpoint controls can still be caught by network monitoring, and traffic that looks suspicious at the network layer can be correlated with device telemetry to identify the source. A mature programme operates both layers in concert.
Why Network Security Still Matters in the Cloud Era
Network security has not become less important in a cloud-first environment. It has changed shape. Three forces keep it on the cyber security shortlist for NZ SMEs: the dissolution of the traditional perimeter has produced more boundaries to defend rather than fewer, hybrid environments connect multiple networks that each need protection, and the formalisation of network controls as a compliance and insurance expectation continues to firm up.
The perimeter has shifted, not disappeared
In a traditional setup there was one network boundary to defend: the office firewall. Today there are many: the office connection, every home worker’s connection, the path to each cloud service, the link to every partner, the public-facing services exposed to the internet. Each one needs controls. The total surface to defend is larger now, not smaller, even though the shape is less neat.
Layered defence has become the operating reality. Our blog on Defence in Depth covers why multiple overlapping controls produce a stronger outcome than any single perimeter, and where the network sits within that thinking.
Hybrid environments need protection at every boundary
Most NZ SMEs now run a hybrid mix of on-premises systems, cloud services, and SaaS applications. Traffic flows between all of them: staff devices reach cloud services, cloud services reach on-premises systems, partner networks reach internal applications. Each path is a potential attack route. Modern network security covers all of these boundaries with consistent policies rather than treating each one as a separate problem.
Insurance, compliance, and customer expectations
Cyber insurers expect basic network controls (modern firewalls, segmentation, monitoring) on every business policy. Auditors expect them for NZ Privacy Act compliance on systems handling personal data. Customers ask about network controls in their security questionnaires before signing contracts. The commercial cost of weak network defences has shifted from “potential risk” to “concrete competitive disadvantage”.
Network downtime or compromise is also one of the most common triggers for invoking a Business Continuity Plan. The two disciplines reinforce each other: better defences reduce the likelihood of needing to invoke continuity procedures.

The Layers of Modern Network Security
Modern network security is built from five complementary layers, each addressing a different attack pattern. Next-generation firewalls inspect deep into connections, intrusion prevention identifies and blocks attack patterns, secure web gateways and DNS filtering stop users reaching malicious destinations, segmentation limits lateral movement, and secure remote access replaces flat VPN connectivity with policy-driven, identity-aware controls.
Next-generation firewalls (NGFW)
Next-generation firewalls go far beyond the port-and-protocol filtering of the old generation. They inspect the actual content of each connection, identify applications (recognising Microsoft 365 traffic as different from generic HTTPS), integrate with user identity systems, and apply policy based on what is happening rather than just where it is happening. Modern offerings from Fortinet, Palo Alto, Cisco, and Sophos are all capable platforms for NZ SMEs at different price points.
Intrusion detection and prevention
Intrusion detection systems (IDS) watch traffic for patterns that match known attacks. Intrusion prevention systems (IPS) actively block what they detect. Both rely on continuously updated threat intelligence to stay current as attackers change tactics. Most modern firewalls include integrated IPS capability, which means most NZ SMEs already have the underlying technology and simply need to ensure it is configured and updated.
Secure web gateways and DNS filtering
Secure web gateways inspect outbound web traffic from staff devices, blocking access to known malicious sites, filtering by category (preventing access to gambling or adult content where business policy demands it), and inspecting downloads for malware. DNS filtering performs a similar role by blocking name resolution for malicious domains. Both stop the most common attack delivery routes at their source.
Network segmentation
Segmentation divides the internal network into isolated zones with explicit policies about what can communicate with what. A compromised laptop in the marketing segment cannot reach the finance servers in the next segment without being verified. Modern microsegmentation can apply this at very fine granularity, even between individual workloads. The result is that one compromise stays one compromise instead of spreading.
Secure remote access and zero trust network access
Traditional VPN gives a connected user broad network reach by default. Zero trust network access (ZTNA) replaces this with per-application access that is continuously verified against identity, device health, and risk signals. Cloudflare Access, Microsoft Entra Application Proxy, and Zscaler ZPA are common options. For NZ SMEs with staff working from anywhere, the shift from VPN to ZTNA is one of the most impactful network security improvements available.
How Network Security Works in Practice
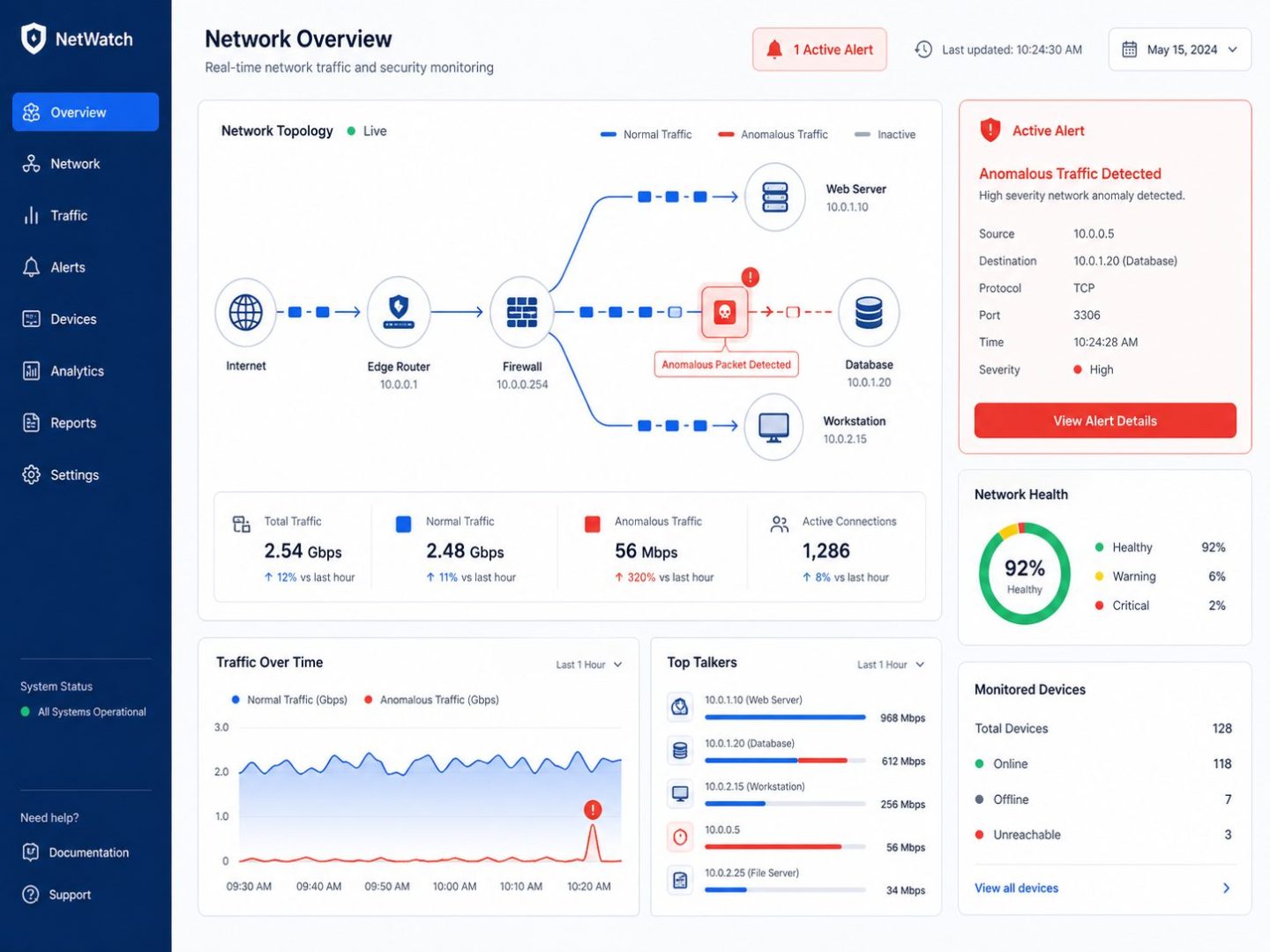
In practice, network security delivers continuous protection through four operational behaviours: inspecting traffic in detail, integrating threat intelligence in near real time, logging and monitoring everything for later analysis, and responding actively when an attack is confirmed. The layers above provide the capabilities; these behaviours turn them into an active defence.
Traffic inspection and filtering
Every connection passing through the controls is inspected against policy. Source and destination, application type, user identity, content (where decryption is enabled), and behavioural patterns all factor into the decision. Allowed traffic flows freely; suspicious traffic is logged for review; clearly malicious traffic is blocked outright. The inspection runs at line speed on modern hardware, so there is no operational penalty for the user.
Threat intelligence integration
Modern controls subscribe to continuously updated feeds of known-malicious indicators: bad IP addresses, malware command-and-control servers, phishing infrastructure, and emerging campaign patterns. The feed updates flow into the rule sets automatically, often within minutes of new threats being identified anywhere in the world. This means the defence is current rather than static.
Logging and continuous monitoring
Every decision the network makes is logged: connections allowed, connections blocked, anomalies flagged, policies updated. These logs feed into security operations centres (internal or outsourced) where they are correlated with endpoint, identity, and application telemetry. Pattern analysis across these sources detects multi-stage attacks that no single control could have caught alone.
Active response and containment
When a confirmed threat is detected, the controls do not just alert; they respond. Suspicious connections are dropped, source addresses are blocked, infected hosts are isolated from sensitive segments, and security teams are notified to investigate. The faster this happens, the less damage spreads. Automation now handles the first wave of response in seconds, with humans making the higher-order decisions that follow.
How to Build a Network Security Programme
Building a working network security programme is a sequence of focused phases rather than a single project. The work runs through five stages: map the network, deploy core controls, segment and isolate, monitor continuously, and test and improve. Skipping the mapping phase is the most common cause of incomplete protection.
Step 1: Map the network
Document every connection point, every service exposed to the internet, every link between sites, every VPN entry, and every cloud-to-on-premises connection. Most NZ businesses doing this for the first time find connections nobody had on the list: a long-forgotten port forward, a contractor VPN that should have been turned off, a cloud service connecting back to the corporate network for reasons nobody can explain. The map is the foundation; everything else builds on it.
Step 2: Deploy modern core controls
Replace any legacy firewalls with next-generation alternatives, enable integrated intrusion prevention, deploy DNS filtering across the business, and add secure web gateway capability for outbound traffic. Most NZ SMEs cover this with one or two vendors rather than buying every layer separately. The aim is consistent policy rather than the most boxes.
Step 3: Segment and isolate
Carve the network into segments based on what each part actually needs to do. Office staff in one segment, servers in another, guest WiFi entirely separate, IoT devices in their own zone, customer-facing services in a DMZ. Apply explicit policies for what can talk to what. The work takes weeks rather than months for most NZ SMEs and dramatically reduces the blast radius of any compromise.
Step 4: Monitor continuously
Send logs from every control into a central platform where they can be correlated and analysed. Most NZ SMEs do this through a managed detection and response service rather than building internal capability from scratch. The monitoring catches what point controls miss and turns a collection of products into a coherent defence.
A continuously monitored network is also a more resilient one. Cyber Resilience depends on the ability to detect problems quickly and respond before they escalate, which is precisely what good monitoring delivers.
Step 5: Test and improve
Annual penetration tests, quarterly configuration reviews, and continuous attack surface monitoring keep the programme honest. Configurations drift, new services appear, and attackers change tactics. Without periodic testing and adjustment, defences that were strong last year may have quietly weakened. The right cadence is more frequent than most businesses expect.
Common Network Security Mistakes
A handful of mistakes recur across NZ businesses and each one quietly undermines the value of any investment. Recognising them early prevents the slow drift from active defence back into “we have a firewall, we are fine”.
Flat networks with no segmentation
Many NZ SMEs still run a single flat network where everything can talk to everything. Once an attacker gets in anywhere, they can reach anywhere. The fix is segmentation. The work is not trivial but it is finite, and the security improvement is dramatic. Starting with simple separations (guest WiFi, IoT zone, server segment) delivers most of the value in the first month.
Old firewalls that nobody tunes
A firewall installed five years ago and never touched since is barely defending against current attacks. Rules accumulate, threats evolve, and configurations drift. Modern next-generation firewalls need active tuning: regular rule reviews, threat intelligence updates, and policy adjustments as the environment changes. A neglected firewall produces a false sense of security that is worse than honest weakness.
VPN as the only remote access path
Traditional VPN gives a connected user broad network reach. A compromised account or device with VPN access can move freely across the internal network. Replacing VPN with zero trust network access for most use cases produces dramatically tighter network security and better user experience at the same time. VPN remains useful for some specific scenarios, but as the default for everyday remote access it is showing its age.
No visibility into what actually flows
Without logging and monitoring, the controls become a black box. Things either work or they do not, and there is no way to investigate when something goes wrong. The fix is to enable logging on every control, send the logs somewhere they can be analysed, and review the patterns regularly. Most useful threat detections come from pattern analysis across multiple sources rather than from any single device alarm.
Get the Right Network Defences in Place
Network security has changed shape over the past decade but remains foundational to any serious cyber defence. Done well, it stops the majority of attacks at the edge and provides the visibility to handle the rest before they cause harm. Done badly, it produces a false sense of safety while leaving the highway wide open. Exodesk works with businesses across Christchurch, Dunedin, and the South Island to assess existing network posture, design defences that fit the size and shape of the business, and run the day-to-day monitoring and tuning that keeps them effective. Our Cyber Security team covers everything from strategy through implementation and ongoing operations.
Contact us today to discuss how we can help your business or connect with us on LinkedIn to stay updated with more insights.
Frequently Asked Questions
What is network security in simple terms?
Network security is the discipline of protecting the connections, traffic, and devices that make up a business network from unauthorised access, attack, and misuse. It includes firewalls, intrusion prevention, secure remote access, segmentation, and continuous monitoring. The goal is to stop threats at the edge before they reach business systems and to detect anything that gets through.
Why is network security important for businesses?
Network security matters because the network carries every piece of business data, every staff login, every customer transaction, and every attempted attack. Defending the network protects everything that uses it. As businesses spread across cloud services, home offices, and partner connections, the discipline has become more important rather than less, with more boundaries to defend than ever.
What are the main types of network security?
The main types are next-generation firewalls, intrusion detection and prevention systems, secure web gateways and DNS filtering, network segmentation, and secure remote access (zero trust network access replacing traditional VPN). Most modern network security programmes combine all of these layers rather than relying on any single one.
What is the difference between network security and cyber security?
Cyber security is the broader discipline that covers protecting systems, data, and people from cyber threats across every dimension. Network security is one specific area within cyber security that focuses on protecting the connections and traffic between systems. Network security is a major component of cyber security, alongside endpoint, identity, application, and data security.
What is the difference between network security and endpoint security?
Endpoint security protects individual devices (laptops, phones, servers) from attack. Network security protects the connections between those devices and the systems they reach. The two are complementary: endpoint controls catch threats on the device, network controls catch threats in transit, and the combination produces a stronger defence than either alone.
How much does network security cost?
Costs vary widely with the size of the network, the platforms chosen, and whether monitoring is run internally or through a managed service. Annual subscription pricing on firewalls and security platforms is the most common model. Vendor pricing changes regularly, so current figures should come from a scoped assessment rather than older sources. The dominant cost is usually monitoring and management rather than the hardware itself.
What is a firewall and is it enough?
A firewall is a device or software that controls traffic between networks based on policy. A modern next-generation firewall is a substantial part of network security, but it is not enough on its own. Effective protection layers intrusion prevention, DNS filtering, segmentation, secure remote access, and monitoring on top of the firewall. The combination is what catches the threats a single product would miss.
What is network segmentation?
Network segmentation divides an internal network into isolated zones with explicit policies about what can communicate with what. A compromised device in one segment cannot freely reach systems in another segment without being verified. The result is that one compromise stays one compromise instead of spreading laterally across the entire environment. Segmentation is one of the highest-impact network security improvements available.
Does moving to the cloud reduce the need for network security?
No. Cloud changes the shape of the network rather than removing it. Traffic still flows between users, devices, cloud services, and on-premises systems, and each flow needs protection. Some controls move into cloud-native form (cloud firewalls, secure access service edge platforms) but the underlying discipline of inspecting traffic and verifying connections remains essential.
How do we improve our network security?
Start with an honest map of the existing network and its connections. Replace legacy firewalls with modern alternatives, enable DNS filtering and intrusion prevention, implement segmentation between zones with different sensitivity levels, replace VPN with zero trust network access where possible, and set up continuous monitoring across the whole environment. An experienced IT partner can typically have meaningful improvements in place within weeks.