| Cyber resilience is the ability of a business to anticipate, withstand, recover from, and adapt to cyber attacks — without suffering irreversible damage to operations, data, or reputation. In 2026, cyber resilience is no longer a best practice for NZ businesses. It is becoming a regulatory expectation. |
The NZ Government released its Cyber Security Strategy 2026-2030 in February this year. It is the most significant national cyber security policy shift New Zealand has seen in a decade. The strategy frames cyber security as a national security challenge and sets a clear expectation that organisations — not just government — must build genuine cyber resilience as part of how they operate.
For South Island businesses, this has direct implications. Whether you operate in healthcare, professional services, finance, construction, or retail, the question is no longer whether you need a cyber resilience strategy. It is whether yours is adequate for what is coming.
| NZ Cyber Security Strategy 2026-2030: cyber threats are a significant national security challenge. The strategy commits to developing a regulatory regime to strengthen the protection of critical infrastructure and proposes introducing civil penalties to the Privacy Act for failures to protect personal information from cyber threats. |
Why Cyber Resilience Has Changed in 2026
Cyber resilience used to mean having backups and an antivirus licence. The threat landscape has changed enough that this framing is now dangerously inadequate.
AI has industrialised cyber attacks. Ransomware is deployed autonomously. Phishing is generated at scale with 80% AI content and 54% click-through rates. Social engineering uses voice clones built from three seconds of audio. The speed, volume, and sophistication of attacks has increased to a point where prevention alone is not a viable strategy. The question is not whether an attack will succeed in reaching your environment — it is whether your organisation can absorb the impact and continue operating.
That is what cyber resilience addresses. And it is why the NZ Government’s 2026 strategy places such emphasis on preparedness and response alongside prevention. Our guide on defence in depth explains how layered security forms the technical foundation of a cyber resilient organisation.
What the NZ Cyber Security Strategy 2026-2030 Means for Your Business
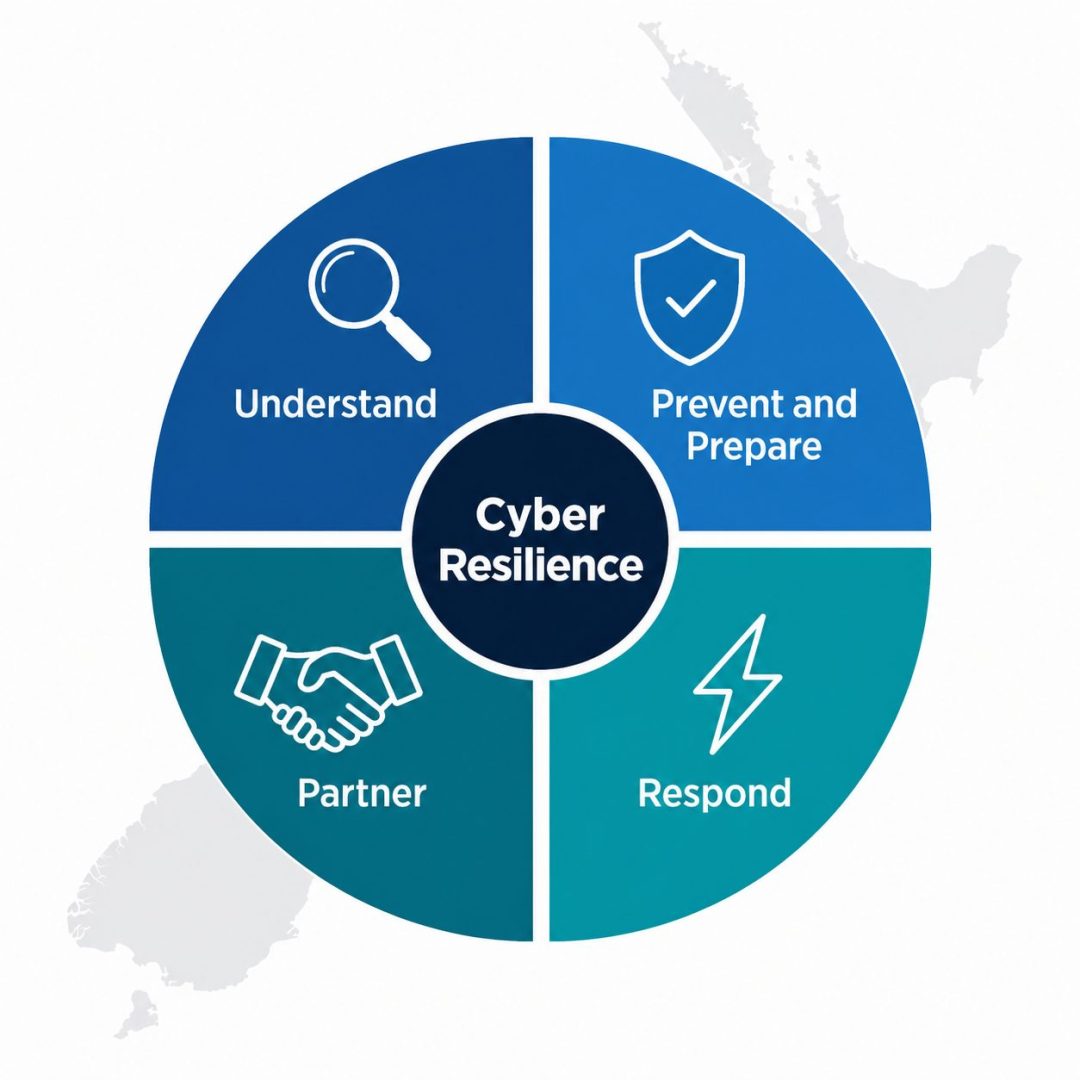
The strategy is structured around four objectives that apply directly to how NZ businesses should be approaching cyber resilience.
| # | Pillar | What It Means for Your Business in 2026 |
| 1 | Understand | Know your cyber risks specifically — not generically. This means asset inventory, threat assessment, and understanding which parts of your business are most exposed. Awareness without specificity does not build resilience. |
| 2 | Prevent and Prepare | Manage cyber risk proactively and be well-prepared for incidents before they occur. This includes tested incident response plans, immutable backups, and staff training — not just technical controls. |
| 3 | Respond | React effectively and decisively when an incident occurs. The strategy’s action plan includes establishing a single national reporting channel through the NCSC to coordinate response. Businesses need their own internal response process to complement this. |
| 4 | Partner | Resilience is bolstered by collaboration. The strategy commits to enhanced threat intelligence sharing between NCSC and industry. Businesses should engage with their IT providers as active partners in resilience — not just reactive helpdesks. |
The strategy also signals regulatory change ahead. The government is actively consulting on mandatory requirements for critical infrastructure cyber resilience, and the Action Plan 2026-2027 proposes advising on civil penalties to the Privacy Act for failures to protect personal information. Organisations in healthcare, finance, energy, and telecommunications should be preparing for these requirements now, not when legislation arrives. More detail on the compliance landscape is in our cybersecurity risk assessment guide.
The Six Elements of Cyber Resilience — Updated for 2026
The original cyber resilience framework — Govern, Identify, Protect, Detect, Respond, Recover — remains the right structure. What has changed is what each element requires in the current threat environment.

1. Govern — make cyber resilience a leadership responsibility
Cyber resilience starts at governance level. The NZ Cyber Security Strategy explicitly signals that cyber security should be treated as a core element of governance, risk management, and strategic decision-making — not delegated entirely to IT.
This means boards and senior leadership need to understand the organisation’s cyber risk exposure, own the risk appetite decision, and ensure adequate resources are allocated to resilience-building activities. Organisations that treat cyber resilience as an IT problem rather than a business problem are consistently less prepared when incidents occur.
2. Identify — know what you are protecting and where it is
You cannot protect what you cannot see. A current asset register covering all devices, software, data stores, cloud services, and third-party integrations is the foundation of cyber resilience. In 2026, shadow IT — unmanaged devices, personal cloud storage, AI tools accessed outside IT oversight — has expanded the attack surface significantly for most businesses.
The NCSC March 2026 warning specifically highlighted credential theft via personal devices and shadow IT as a growing entry point. Understanding your full environment is not a one-time exercise — it requires ongoing visibility. Our dark web monitoring service provides early warning when credentials from your environment have already been compromised.
3. Protect — layer controls, do not rely on any single solution
Protection in 2026 requires layered controls because no single tool stops every threat. Email filtering blocks the majority of phishing attempts. Endpoint detection and response catches behavioural anomalies that signature-based tools miss. Multifactor authentication limits credential theft impact. Network segmentation contains lateral movement after an attacker gains initial access.
The NZ Government strategy emphasises visibility, access control, and risk management across cloud-first and distributed environments — a direct acknowledgment that the perimeter-based security model no longer reflects how NZ businesses operate.
4. Detect — assume something has already got through
Cyber resilience requires assuming that some attacks will succeed in reaching your environment. Detection is about finding them before they cause irreversible damage. Modern ransomware operators spend an average of 24 days inside a network before triggering encryption. Continuous monitoring that detects unusual access patterns, file encryption behaviour, or anomalous data movement can surface an intrusion during that window.
Effective detection requires 24/7 monitoring — not business-hours coverage. This is one of the key reasons businesses outsource security monitoring to a managed IT provider. Our managed IT services include continuous monitoring across endpoints, network, and cloud environments.
5. Respond — a plan that has never been tested is not a plan
The strategy commits to improving coordinated incident response across NZ through the NCSC’s new single reporting channel. For businesses, this means having your own internal response process ready to activate before you reach out to external support.
A tested incident response plan defines who makes decisions, who communicates with staff and clients, how affected systems are isolated, and what the Privacy Act notification obligations are if personal data has been compromised. NZ cyber security research shows that fewer than one third of NZ organisations have a tested plan — a gap that directly correlates with longer recovery times and higher costs.
Our business continuity planning guide covers what a tested plan looks like and the specific steps that make the difference between a managed incident and an uncontrolled one.
6. Recover — resilience is measured by how fast you restore operations
Recovery is the measure of cyber resilience that matters most. Businesses that recover in hours demonstrate genuine resilience. Businesses that take months demonstrate the cost of under-investment in the other five elements.
Recovery capability depends directly on backup quality, documentation, and the existence of a tested restore process. Immutable backups — copies that cannot be altered or deleted by a compromised account — are the non-negotiable foundation. The 3-2-1-1 rule (three copies, two media types, one offsite, one offline) provides the depth needed to recover from the scenarios most likely to affect NZ businesses.
The Cyber Resilience Challenges Specific to NZ SMEs
Larger organisations have dedicated security teams, compliance functions, and enterprise budgets. For South Island SMEs, building cyber resilience requires pragmatic prioritisation.
Limited IT resources
Most NZ SMEs do not have internal IT security expertise. A managed IT provider who understands cyber resilience — not just break-fix support — fills this gap without the overhead of a full-time hire. The key is choosing a provider whose model incentivises prevention rather than billing for incidents.
Third-party risk
NZ businesses depend on suppliers, software vendors, and cloud services. Each third party represents a potential entry point. The NZ Cyber Security Strategy specifically identifies managing high-risk vendors across the public sector as a priority — a principle that applies equally to private sector organisations. A cyber resilient business has visibility into its third-party dependencies and has assessed the risk each one represents.
Keeping pace with the threat
The threat landscape changes faster than most business review cycles. AI-powered attacks that were emerging threats in 2024 are now operational at scale in 2026. Cyber resilience requires continuous improvement — not a one-time implementation that is revisited annually at best.
Is Your Business Genuinely Cyber Resilient?
Exodesk has helped South Island businesses build cyber resilient operations from our offices in Christchurch and Dunedin since 1989. Our fixed-price managed IT services cover the monitoring, protection, backup, and incident response planning that turn a theoretical cyber resilience strategy into a practical, tested capability.
If your current cyber resilience approach was built before the NZ Cyber Security Strategy 2026-2030 and the current AI threat landscape, it is worth reviewing what has changed and where gaps exist.
Contact us today to discuss how we can help your business or connect with us on LinkedIn to stay updated with more insights.
Frequently Asked Questions About Cyber Resilience
What is cyber resilience?
Cyber resilience is the ability of a business to anticipate, withstand, recover from, and adapt to cyber attacks without suffering irreversible operational, financial, or reputational damage. It goes beyond cyber security — which focuses on preventing attacks — to encompass how well an organisation can continue functioning and restore normal operations when an attack succeeds.
What does the NZ Cyber Security Strategy 2026-2030 mean for NZ businesses?
Released in February 2026 by the Department of Prime Minister and Cabinet, the strategy frames cyber security as a national security challenge and sets a clear expectation that businesses must build genuine cyber resilience. The accompanying Action Plan 2026-2027 signals regulatory change including potential mandatory requirements for critical infrastructure and proposed civil penalties in the Privacy Act for failures to protect personal information. Businesses in regulated sectors should be preparing now rather than waiting for legislation.
What is the difference between cyber security and cyber resilience?
Cyber security focuses on preventing attacks from succeeding. Cyber resilience accepts that some attacks will reach your environment and focuses on your ability to detect, contain, respond to, and recover from them without catastrophic damage. A cyber secure organisation has strong preventive controls. A cyber resilient organisation can absorb an attack and continue operating — which is the standard that the 2026 NZ strategy explicitly requires.
What are the six elements of cyber resilience?
The six elements are Govern — making cyber resilience a leadership responsibility; Identify — knowing your assets and exposure; Protect — layering technical controls; Detect — monitoring for threats that get through; Respond — activating a tested incident response plan; and Recover — restoring operations quickly from clean backups. Each element is interdependent — weakness in any one significantly undermines the others.
How does AI change the cyber resilience requirements for NZ businesses?
AI has increased the speed, volume, and sophistication of attacks to a point where prevention alone is not sufficient. Ransomware is now deployed autonomously. Phishing is generated at scale with near-perfect personalisation. Voice cloning enables social engineering attacks that bypass human detection. Cyber resilience in 2026 requires the assumption that some attacks will reach your environment and a tested capability to detect and respond before irreversible damage occurs.
What is the 3-2-1-1 backup rule for cyber resilience?
The 3-2-1-1 rule specifies three copies of your data, stored on two different media types, with one copy offsite and one copy offline or air-gapped. The additional 1 — the offline copy — is the critical addition for cyber resilience, as ransomware operators specifically target and delete cloud and network-connected backups before triggering encryption. An air-gapped copy inaccessible via compromised credentials provides the clean restore point that makes recovery possible.
Do NZ small businesses need to worry about the NZ Cyber Security Strategy?
Yes. While the strategy’s regulatory proposals focus initially on critical infrastructure sectors, the strategy adopts a whole-of-society approach that explicitly includes businesses of all sizes. The proposed Privacy Act changes — introducing civil penalties for failures to protect personal information — will apply broadly. Any NZ business holding customer or employee data has compliance exposure, and the government’s direction is clearly toward higher rather than lower cyber security expectations over the next five years.
What is a tested incident response plan and why does it matter for cyber resilience?
A tested incident response plan is a documented, rehearsed procedure for how your organisation detects, contains, investigates, and recovers from a cyber incident. It specifies who makes decisions, how staff and clients are communicated with, how affected systems are isolated, and what regulatory notifications are required under the NZ Privacy Act. NZ research shows fewer than one third of organisations have a tested plan — those that do recover significantly faster and at lower cost than those that do not.
How does a managed IT provider help build cyber resilience?
A managed IT provider contributes to cyber resilience by delivering 24/7 monitoring, patch management, endpoint protection, email security, backup management, and incident response planning — the technical foundations of the Protect, Detect, Respond, and Recover elements of the framework. For NZ SMEs without internal security expertise, a managed provider fills the gap at a predictable monthly cost that is significantly lower than the cost of a cyber incident.
How does Exodesk help NZ businesses build cyber resilience?
Exodesk works with South Island businesses from our offices in Christchurch and Dunedin to build cyber resilient operations covering all six elements of the framework. Our fixed-price managed IT services include continuous monitoring, layered security controls, immutable backup management, staff security awareness training, and tested incident response planning. We work as a genuine IT partner — not just a helpdesk — to ensure that when an incident occurs, your business can absorb and recover rather than collapse.